Three essays on hacking - Stripe Partners.
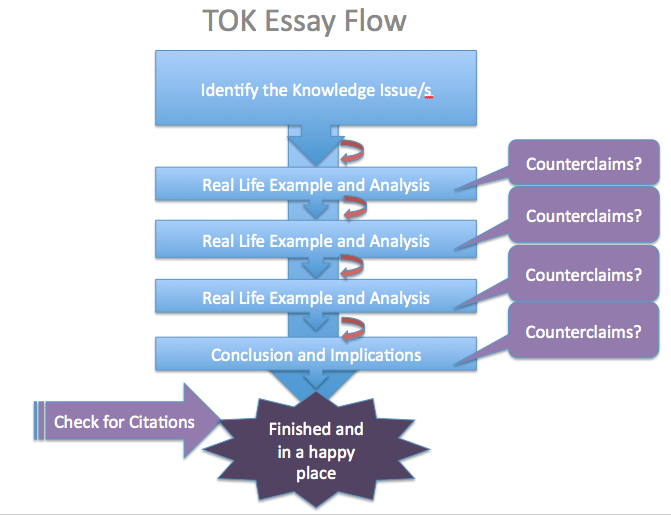
For example, in my essay, I use two examples that show how it's good if you do pay attention to details, but then I also use an example which shows why it is so bad if you do NOT pay attention to details. The content on Tiny Buddha is designed to support, not replace, medical or psychiatric treatment.
One example shows you how to paraphrase in your introduction. Buy an essay online cheap essay that I want Considering that many admissions officials will review dozens or even hundreds of applications a day, standing out buy an essay online cheap the crowd can massively improve your chance of admission.
Other posts on the site.
Essay on the book the color purple. Letters and sounds homework phase 2. Day nursery business plan sample. How to write a review essay on a book. Free e thesis online. Horse related essay topics. Cold mountain analysis essay. Band 9 essays simon. Persuasive essay for 9th graders. Do my english homework. Descriptive essay playing piano.
Hacking is a process in which one uses a computer or computer program to manipulate or exploit the weakness in a network system or a computer for the main purpose of causing harm, fear or make money. And a person who does this is called a hacker. Hacking was first made popular by the M.I.T engineers during late 1950’s and early 1960’s.
Examples of research proposal. Using a research proposal example is quite a typical practice for most of the students, as it helps them to save time and get a better understanding of the assignment. A sample research proposal helps scholars to get familiar with the paper’s structure, its key elements and size.
Essay on hacking. Essay On HAckingby Philip smith. A topic that i know very well is computers and computer hacking. Computers. seem very complicated and very hard to learn, but, if given time a computer can be very. useful and very fun. Have you ever heard all of that weird computer terminology? for and. example, Javascript.
Once the hacker had control, the zombie would be incorporated into a botnet. Of all the infected computer systems, approximately 20% were successfully assimilated into the malicious network. That put the estimated size of the botnet ZeroAccess was responsible for creating at 1.9 million computers as of August 2013, according to Symantec.